Imagine sending money to someone across the globe without a bank, a payment processor, or any middleman checking your balance. That is exactly what Bitcoin is a decentralized digital currency that enables direct peer-to-peer transactions without central authorities was designed for. But how does it actually work? How do thousands of strangers agree on who owns what without a CEO calling the shots?
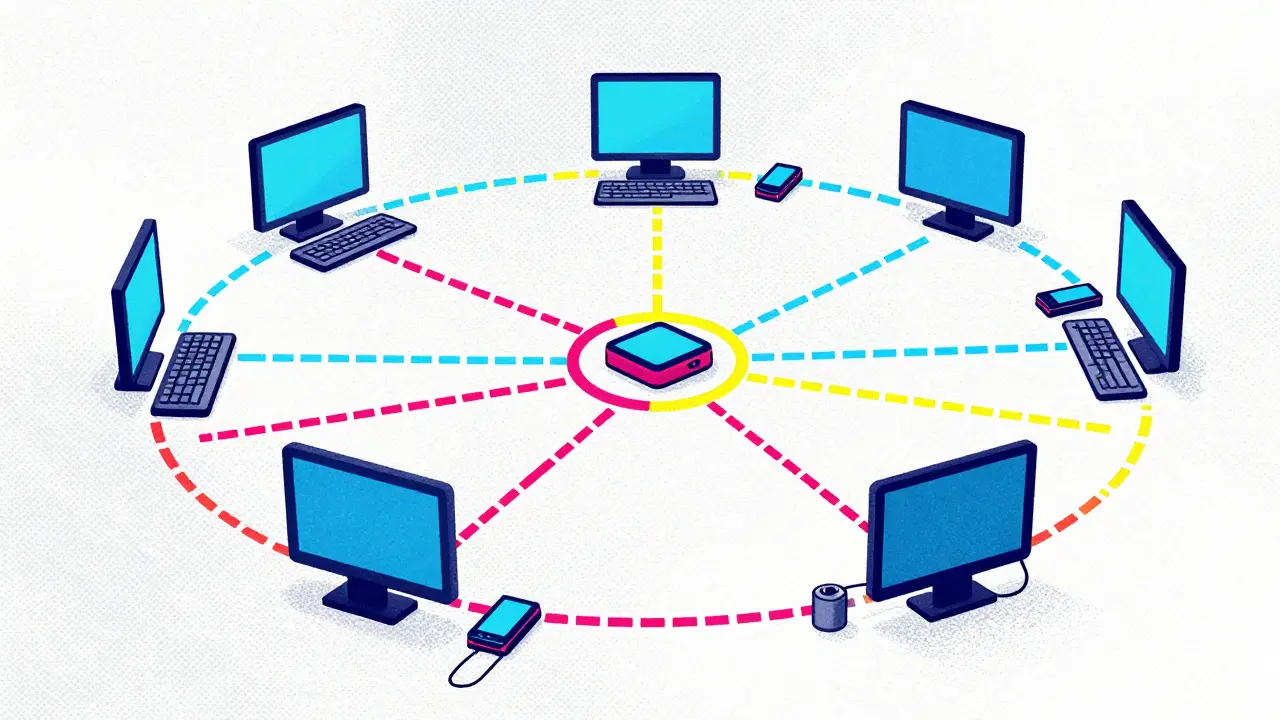
The answer lies in the **Bitcoin P2P network**. This isn't just a fancy term for "online chat." It is a robust, decentralized infrastructure where every participant acts as both a client and a server. There are no master servers. There are no single points of failure. Just a mesh of computers talking to each other, verifying data, and keeping the ledger alive.
The Core Architecture: No Masters, Only Peers
To understand the Bitcoin P2P network, you first have to forget how traditional internet services work. When you visit a website, your computer (the client) asks a specific server for information. If that server goes down, the site is gone. Bitcoin flips this model entirely.
In the Bitcoin ecosystem, every connected computer is called a full node is a computer that stores a complete copy of the blockchain and validates all transactions according to consensus rules. These nodes form a flat hierarchy. Your node doesn't care if it's talking to a university supercomputer or a Raspberry Pi running in someone's garage. They all have equal status.
This design creates three major benefits:
- Censorship Resistance: No one can block a transaction because there is no central gatekeeper.
- Fault Tolerance: If half the nodes vanish overnight, the network keeps running. The remaining peers automatically pick up the slack.
- Trustlessness: You don't need to trust a bank. You only need to trust the code and the majority of the network's computing power.
Each node identifies itself using a unique triple: an IP address, a port number, and a node ID. This ensures that even if two people use the same hardware model, their identities on the network remain distinct. The system is built to handle chaos, not order.
Bootstrapping: How New Nodes Find Friends
Here is a tricky problem: If you download Bitcoin software today, your computer knows nothing about the network. It has no friends. It has no contacts. How does it find other nodes to connect with? This is known as the bootstrap problem.
Satoshi Nakamoto, Bitcoin's creator, solved this with a multi-layered discovery strategy that is surprisingly resilient. First, your node queries DNS seed servers are distributed domain name systems operated by independent entities that provide initial lists of active Bitcoin node IP addresses. There are currently nine independent DNS seeds run by different people around the world. This diversity is crucial. If one operator gets hacked or shuts down, the others keep the network accessible.
If those DNS seeds fail, the system falls back to seed nodes are hard-coded IP addresses of well-maintained public nodes included in the Bitcoin Core software distribution. These are literally baked into the software code in a file called chainparamsseeds.h. They act as emergency lifelines. Even if the entire internet seemed hostile, these hard-coded addresses give new nodes a foothold.
For users who want extra privacy or live in censored regions, the network also supports Tor is an anonymity network that allows Bitcoin nodes to communicate via onion routing to hide their physical location and IP address and I2P networks. This means you can join the P2P network without revealing your real IP address to your peers, adding another layer of security against targeted attacks.

Data Flow: Blocks, Transactions, and Validation
Once a node connects to its peers, the real work begins. The Bitcoin P2P network is essentially a gossip protocol. When a new transaction occurs, it doesn't go to a central database. Instead, the originating node broadcasts it to its immediate peers. Those peers verify the transaction against the consensus rules (e.g., does the sender have enough funds? Is the signature valid?) and then relay it to their peers. Within seconds, the transaction propagates across the globe.
Blocks follow a similar path but with stricter validation. Miners bundle transactions into blocks and broadcast them. Full nodes download every block, verify every transaction inside it, and check the proof-of-work hash. Only if everything checks out do they add the block to their local copy of the blockchain and tell their neighbors, "Hey, I found a new block!"
This process creates two types of node behaviors:
- Archival Nodes: These store the entire history of the blockchain from 2009 to present. As of 2025, this requires approximately 400-500 GB of storage space. They serve historical data to other nodes.
- Pruned Nodes: These validate every transaction but delete old block data after verification. They save disk space while maintaining the ability to enforce consensus rules.
Both types contribute to the network's health. Archival nodes ensure historical integrity, while pruned nodes allow more people to participate with limited hardware resources.
P2P vs. Client-Server: Why Decentralization Matters
Let's compare Bitcoin's P2P network to traditional banking systems. In a bank's system, all transaction records live on centralized servers. If hackers breach those servers, millions of accounts are at risk. If the government orders the bank to freeze assets, they can do it instantly. The system is efficient but fragile.
| Feature | Bitcoin P2P Network | Traditional Banking System |
|---|---|---|
| Control | Distributed among all nodes | Centralized authority (bank/government) |
| Fault Tolerance | High (network survives partial failures) | Low (single point of failure risks) |
| Censorship | Impossible to centrally block transactions | Easily enforced by administrators |
| Scalability | Limited by bandwidth and propagation speed | Highly scalable with dedicated infrastructure |
| Transparency | All transactions visible to anyone | Private ledgers known only to the institution |
The trade-off is clear. Bitcoin sacrifices raw speed and convenience for sovereignty and security. You cannot force a network update on all nodes like a software company pushes a patch. Every change must be agreed upon by the majority through consensus. This makes evolution slow, but it prevents malicious actors from hijacking the system.

Running a Node: Practical Considerations
You might think, "I'll run my own node to support the network." That's great, but it requires resources. Running a full Bitcoin node isn't just clicking "install." Here is what you need to know:
- Storage: Expect to dedicate 500+ GB of SSD space. HDDs work but are slower for verification.
- Bandwidth: You will upload and download several gigabytes of data daily. Unlimited plans are recommended.
- Uptime: Nodes should stay online 24/7. Frequent disconnects hurt your reputation as a reliable peer.
- Initial Sync: Downloading and verifying the entire blockchain takes hours or days depending on your internet speed. Patience is key.
If this sounds too technical, many users opt for SPV clients are Simplified Payment Verification wallets that connect to full nodes to verify transactions without downloading the entire blockchain. These lightweight wallets save space and time but rely on third-party nodes for data. You trade some privacy and security for convenience. For most casual users, this is fine. For those who want true sovereignty, running a full node is worth the effort.
Future Challenges and Innovations
The Bitcoin P2P network is not static. It faces ongoing challenges, particularly scalability. As more people use Bitcoin, the size of blocks grows, straining bandwidth and storage. To solve this, developers have introduced second-layer solutions like the Lightning Network is a layer-2 scaling protocol built on top of Bitcoin that enables instant, low-cost micro-transactions off-chain. Lightning maintains P2P principles but moves small payments off the main blockchain, reducing congestion.
Protocol upgrades like Taproot and Schnorr signatures have also improved efficiency, allowing more complex transactions to fit into blocks without increasing size. Meanwhile, projects like Dandelion++ enhance privacy by obscuring the origin of transactions during the relay phase, making it harder for observers to map the network topology.
Despite regulatory pressures in some countries, the decentralized nature of the P2P network makes it nearly impossible to shut down. Governments can ban exchanges or restrict mining, but they cannot stop individuals from connecting to peers and validating transactions. This resilience is why Bitcoin remains the gold standard for decentralized finance.
What happens if I disconnect my Bitcoin node from the P2P network?
If you disconnect your node, you lose the ability to independently verify transactions and blocks. You won't receive new blocks until you reconnect. The rest of the network continues operating normally; your absence has minimal impact due to the large number of other nodes. However, your wallet may show outdated balances until you resync.
Do I need to run a full node to send Bitcoin?
No. Most users rely on mobile wallets or web-based services that connect to full nodes on their behalf. These SPV clients allow you to send and receive Bitcoin without storing the entire blockchain. However, running your own node gives you greater control, privacy, and independence from third-party services.
How does the Bitcoin P2P network prevent double-spending?
Double-spending is prevented through consensus. When a transaction is included in a block, all nodes verify that the inputs haven't been spent before. Once the block is added to the chain and confirmed by subsequent blocks, the transaction is considered irreversible. The distributed nature of the network ensures that no single entity can alter past transactions without controlling the majority of the network's computing power.
Why are DNS seeds important for the Bitcoin network?
DNS seeds are critical for bootstrapping new nodes. They provide a decentralized way to discover active peers without relying on a single source. If DNS seeds were controlled by one entity, that person could censor new nodes or spread malicious software. By distributing control among multiple operators, the network remains resilient against manipulation and failure.
Can the Bitcoin P2P network be attacked?
Yes, but it is difficult. Attackers can attempt eclipse attacks by isolating a node and feeding it false information, or Sybil attacks by creating many fake nodes to influence peer selection. However, the network's reliance on multiple discovery methods (DNS seeds, hard-coded seeds, Tor) and strict validation rules makes successful attacks rare and costly. The decentralized structure naturally resists coercion and censorship.